byTINTSWALO BALOYI
JOHANNESBURG – AS cybercriminals grow more sophisticated and corporate networks become increasingly complex, organisations face mounting risks from advanced persistent threats, ransomware, data breaches, and insider attacks.
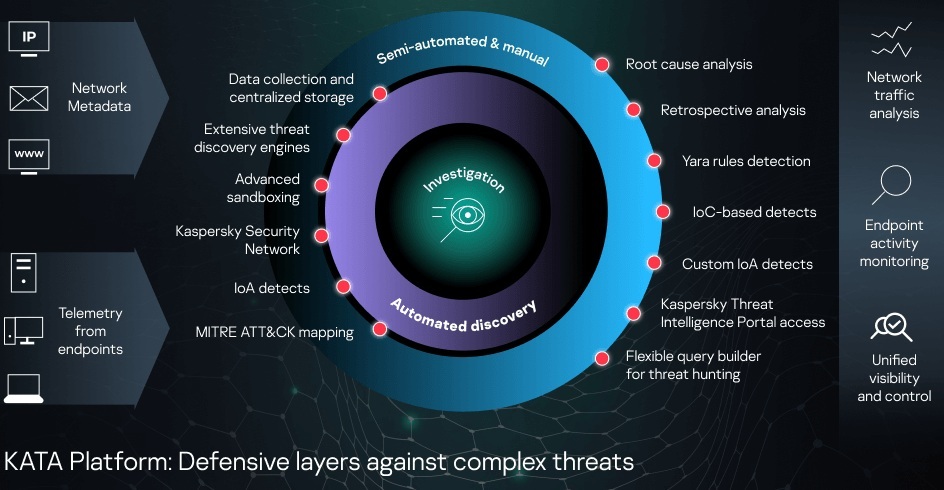
In response to this evolving danger landscape, Kaspersky has released Kaspersky Anti Targeted Attack 8.0 (KATA 8.0), a major upgrade designed to strengthen Network Detection and Response (NDR) capabilities and improve visibility across enterprise IT environments.
Modern businesses operate in highly distributed environments, with cloud services, remote workforces, mobile devices, and third-party integrations expanding the attack surface.
Traditional perimeter-based security models are no longer sufficient. Threat actors now exploit encrypted traffic, compromised credentials, shadow IT services, and misconfigured systems to infiltrate networks undetected.
Without deep network visibility and intelligent threat detection, organisations risk financial losses, operational disruption, reputational damage, and regulatory penalties. Early detection and rapid response are critical to limiting the impact of breaches.
KATA 8.0 introduces enhanced anomaly detection technology that analyses key protocols frequently abused in cyberattacks, including DNS, HTTP, and Kerberos.
Rather than scanning all traffic indiscriminately, the system identifies deviations specific to each organisation’s infrastructure and behavioural patterns.
This focused approach improves detection accuracy while reducing false positives — a major cause of alert fatigue in security teams.
To address risks posed by unauthorised applications, KATA 8.0 includes shadow IT detection, enabling organisations to identify the use of more than 5,000 external public services, including cloud storage and collaboration platforms.
This restores visibility over corporate data flows and helps prevent data leakage.
Retrospective traffic analysis further strengthens investigations. Security teams can upload PCAP files for re-analysis using updated threat intelligence, sandboxing, intrusion detection systems, and anti-malware engines.
This allows previously undetected threats to be discovered after new intelligence emerges.
Importantly, KATA 8.0 collects all network observables — including file names, URLs, and hashes — not just confirmed malicious objects.
This broader data collection supports proactive investigations and helps identify compromised users before damage escalates.
The platform integrates with endpoint protection, email security, Managed Detection and Response (MDR), and firewall solutions.
Automated file submission, dynamic sandboxing of suspicious attachments, and real-time firewall blocking rules enhance containment and response.
As cyber threats continue to evolve, proactive detection, integrated intelligence, and automated response are no longer optional — they are essential pillars of modern IT security. KATA 8.0 represents a strategic step toward stronger, more resilient network protection in an increasingly hostile digital environment.
– CAJ News